Cyber security in electric vehicle charging stations
Hello People. This article is about cyber security in electric vehicle charging stations. Cyber security in electric vehicle charging infrastructure is a very important aspect. There is a potential for a network of devices to be attacked simultaneously, and the prospective impact that would have on a local distribution network if a large number of devices either attempt to charge or disconnect from the grid at any one time.
Society is getting so used to use devices with connections to the internet for so many daily routines. Electric vehicles (EV) charging infrastructure is as vulnerable to suffer cyber threats as any other connected device. It is crucial, therefore, that the EV sector highlight and tackle the issue of cyber security wherever possible.
Are you looking to start your business in the electric vehicle industry? We provide software development, web application development, mobile application development, charging stations management app, electric vehicle fleet management software development, cyber security and all software services. Please check our home page here https://iwheels.co/

Ok. Let's get back to the article.
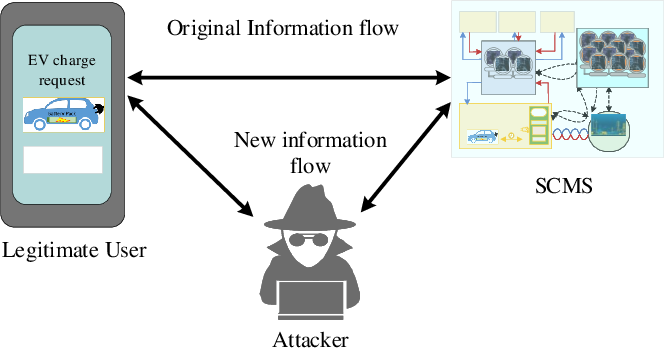
Even if our EV has security protocols and safe algorithms implemented, as well as safety measures, what happens when we plug it in to charge it or we use one of their associated applications? Sometimes there might be security breaches within the electric vehicles charging stations ecosystem that could endanger our privacy, but also our safety and even the entire electric grid infrastructure.
These security weaknesses can affect all the elements that an EV charging station is composed of. From the charging point, the station itself, to the charge point operators (CPO) who provide the charging network infrastructure, as well as the distribution system operators (DSO) that are the operating managers of energy distribution networks.
Implementing cybersecurity measures in each of them is essential to creating a trusted environment where users can experience flawless and secure charging.
Security in EV Charging Station should be especially focused on communication, mobile apps, firmware updates and physical access points. The reason is that, as the charge point and the CPO back-office establish communication with each other, it's important to implement measures to ensure that no one can interfere and alter this communication, which is essential to the proper functioning of the EV charging, by using, for example, encrypted communication.
On the other hand, security should be also strengthened in the mobile apps used to interact with the charging point and the software installed in the station, as these can be easily exposed to cyber threats.
Another important aspect of EV charging station cybersecurity is to support firmware update. It is a process where many vulnerabilities can be identified and corrected to optimize security.
The physical access points of the EV charging stations are exposed to physical attacks, for example by attempting to modify vulnerable software on internal components as microprocessor or memory.
Consequences of an EV charging station
Very different scenarios may occur, but the most frequent scenario will be identity theft, data alteration, unauthorized access privileges, malware insertion, private & sensitive information theft, electricity flow manipulation and changes in operating parameters that may compromise charging stations’ safety among many others.
Moreover, security lack or vulnerabilities in EV charging station makes it possible to launch large-scale cyber-attacks that also compromise security in the power grid. Therefore, not only E-mobility would be in danger, but also the electricity infrastructure itself.
Cybersecurity measures in EV Charging Stations
The power grid is a critical infrastructure and every device that connects to the grid, including EVs and charging stations, needs to provide measures to protect the grid from potential attacks.
Failure of this will result in the loss of user trust in the charging infrastructure if third parties could manipulate massive amounts of charging-related information and billing data from a charging process.
Cybersecurity in EV charging station should include the following measures:
Encryption and decryption of messages to ensure adversary is not able to eavesdrop on the channel to ensure confidentiality.
Verify the integrity of information exchanged.
Verify the communication party (EV or charging point) who it claims to be, in order to ensure authenticity.
Trust model in EV Charging Station
It is important to deploy robust public key infrastructure (PKI). Public Key Infrastructure (PKI) is a hierarchical structure of trusted third parties known as certificate authority (CA).
The primary responsibility of CA is to manage the cryptographic keys used in PKI along with issuance, storage, distribution and revocation of digital certificates. The digital certificates are also known as public key certificates.
A digital certificate is used for verification where vehicle can verify charging station and vice a versa, during handshake, before both the nodes start exchanging information.
Charging station should have integration with CRL to verify if the certificate issued by CA is still valid or not. There can be other relationship based trust model in PKI that can help to verify the digital certificates.
TLS stack on the power line communication (PLC) should support strong cipher suites supporting confidentiality, integrity and authenticity. It is important to understand the need of strong protocol (TLS 1.2) and algorithms power line to avoid data compromise.
ISO 15118 recommends using digital certificates to authenticate and authorize access to charging stations and electric vehicles. The vehicle OEMs and charge point operators must establish sub-CA to issue digital certificates for this purpose. It is highly recommend managing cryptographic keys life cycle in HSMs at the backend to avoid compromise.
The vehicle manufacturer and charge point operator must provide mechanisms to revoke and renew the certificates in case cryptographic keys are compromised.
Conclusion
Therefore, cybersecurity for EV charging station is a critical need due to the high risks, complexity and quick evolution of connected devices we are experiencing nowadays.
Setting a minimum level of security can prevent an attack from resulting in the charging point to malfunction and become a security and safety risk to users, CPO’s and DSO’s.
Hope this article on cyber security in electric vehicle charging stations is useful to you. Continue reading about Things to consider while buying an electric car